API Security
Essential API Security Best Practices for Robust Systems
Updated on:
April 21, 2026

TL;DR
1. Robust API security is non-negotiable, requiring a proactive approach from design to deployment.
2. Foundational practices like strong authentication, authorization, and input validation are critical.
3. Implementing API gateways, rate limiting, and comprehensive monitoring creates essential defense layers.
4. Regular security audits, developer education, and an incident response plan are vital operational best practices.
5. A holistic strategy, embracing both technical controls and organizational diligence, ensures resilient API ecosystems.
A digital landscape, increasingly interwoven by Application Programming Interfaces, presents both unprecedented opportunities and profound vulnerabilities. APIs are the very bedrock of modern connectivity, facilitating everything from mobile applications to microservice architectures and partner integrations. Yet, their pervasive nature makes them prime targets for malicious actors. Overlooking API security is akin to building a magnificent fortress with an open gate; the entire system is at risk. Robust API security isn't merely a technical add-on; it's a fundamental prerequisite for trust, operational continuity, and safeguarding sensitive data in an interconnected world. Embracing strong API security best practices is no longer optional, but an absolute imperative for any organization aiming for resilient, reliable digital operations.
Understanding the API Security Landscape: Why APIs are Prime Targets
The exponential growth in API usage has unfortunately coincided with a sharp increase in API-related cyberattacks. APIs expose critical business logic and sensitive data, making them highly attractive to attackers. Unlike traditional web applications, APIs often lack a human-facing interface, making traditional security tools less effective and requiring a specialized approach to protection. The sheer volume and complexity of API ecosystems mean that a single vulnerability can have cascading effects, compromising entire systems and vast quantities of data. Understanding why APIs are such prime targets is the first step in building an effective defense strategy, one that integrates API lifecycle management with robust security at every stage.
What Makes APIs Vulnerable?
Several inherent characteristics and common development practices contribute to API vulnerabilities:
- Broad Attack Surface: APIs are designed for connectivity, meaning they often expose a wide range of endpoints and functionalities, each a potential entry point for attackers.
- Complex Interdependencies: Modern applications often rely on a mesh of internal and external APIs. A vulnerability in one API can propagate through the entire system.
- Lack of Visibility: Organizations frequently struggle with "API sprawl," losing track of all active APIs, including shadow APIs, making it difficult to secure what isn't fully known.
- Misconfigurations: Incorrectly configured authentication, authorization, or network settings are a common source of breaches.
- Developer Oversight: Developers, often focused on functionality, might inadvertently introduce security flaws if not adequately trained in secure coding practices.
- Data Exposure: APIs frequently handle sensitive data (PII, financial, health), making them high-value targets for data exfiltration.
The OWASP API Security Top 10
The OWASP API Security Top 10 provides a critical framework for understanding and mitigating the most prevalent API security risks. This list, frequently updated, highlights vulnerabilities specifically relevant to APIs, distinguishing them from traditional web application security concerns. Addressing these top risks is a fundamental aspect of comprehensive API security. Key categories include:
- Broken Object Level Authorization: Attackers can bypass authorization by altering the ID of an object in the API request, accessing unauthorized resources.
- Broken User Authentication: Weak authentication schemes, brute-force attacks, or insecure credential management can allow attackers to compromise user accounts.
- Excessive Data Exposure: APIs often return more data than necessary, including sensitive information, which can then be intercepted or exploited.
- Lack of Resources & Rate Limiting: Without proper rate limiting, attackers can overwhelm APIs, leading to denial of service or brute-force attacks.
- Broken Function Level Authorization: Complex access control policies can lead to flaws where authenticated users can access functions they shouldn't.
- Mass Assignment: Clients can guess object properties, sending additional valid properties that the API then accepts, potentially updating unauthorized fields.
- Security Misconfiguration: Common issues include unpatched systems, open cloud storage, unnecessary features, or insecure default configurations.
- Injection: Similar to web apps, APIs are vulnerable to SQL, NoSQL, command, and other injection attacks if input isn't properly validated.
- Improper Inventory Management: Lack of visibility into all APIs, especially shadow or deprecated ones, creates unmonitored attack vectors.
- Unsafe Consumption of APIs: When consuming external APIs, improper validation of responses can lead to vulnerabilities in the integrating application.
Foundational API Security Best Practices
Building a secure API ecosystem begins with implementing a strong foundation of security controls. These are the non-negotiable API security best practices that every organization must adopt to protect their digital assets. Each of these practices serves as a critical barrier against common attack vectors, working in concert to create a resilient defense. Ignoring any of these foundational elements leaves a significant gap in your API's armor. These pillars are fundamental to controlling access to your APIs.
1. Authentication
Verifies the identity of the client making the request. Strong API authentication mechanisms are crucial.
- OAuth 2.0: Ideal for delegated authorization, allowing users to grant third-party applications limited access to their resources without sharing credentials.
- JWT (JSON Web Tokens): Used for securely transmitting information between parties, often in conjunction with OAuth or as a stateless token for API access.
- API Keys: Simple tokens for identifying client applications. While easy to implement, they should be used with caution, typically for public APIs, and always combined with other security measures like rate limiting and IP whitelisting. Effective API key management is vital.
- Mutual TLS (mTLS): Provides two-way authentication, where both the client and server verify each other's identities using TLS certificates, offering a higher level of trust.
2. Authorization
Determines if the authenticated client has permission to perform the requested action on the specific resource. This requires implementing robust access control mechanisms.
- Role-Based Access Control (RBAC): Assigns permissions based on a user's role within an organization.
- Attribute-Based Access Control (ABAC): Provides more granular control by using various attributes (user, resource, environment) to define permissions.
- Granular Permissions: Ensure that users/applications only have access to the exact resources and actions they need, adhering to the principle of least privilege.
3. Input Validation and Sanitization
All data received from clients must be treated as untrusted. Rigorous input validation and sanitization are essential to prevent common attacks like:
- SQL Injection: Malicious SQL statements inserted into input fields to manipulate database queries.
- Cross-Site Scripting (XSS): Injecting malicious scripts into content that is then served to other users.
- Command Injection: Executing arbitrary commands on the server.
- XML External Entity (XXE) Attacks: Exploiting vulnerabilities in XML parsers to access files or perform DoS.
- Mass Assignment: Prevents clients from supplying unwanted properties in their requests that could overwrite sensitive data.
Validate data types, formats, length, and content against a strict schema. Sanitize input by encoding or escaping special characters before processing or storing them.
4. Data Encryption In Transit and At Rest
Encryption is crucial for protecting sensitive data wherever it resides:
- Encryption in Transit: Always use HTTPS (HTTP over TLS/SSL) for all API communication. This encrypts data as it travels between the client and server, preventing eavesdropping, tampering, and Man-in-the-Middle (MitM) attacks. Ensure strong TLS versions and ciphers are used.
- Encryption At Rest: Encrypt sensitive data stored in databases, file systems, or cloud storage. This protects data even if an attacker gains access to the underlying storage infrastructure. Use strong encryption algorithms and secure key management practices.
5. Rate Limiting and Throttling
Implementing limits on API requests is vital for both security and stability. API rate limiting and throttling prevent:
- Denial of Service (DoS) and Distributed DoS (DDoS) Attacks: Overwhelming the API with excessive requests, making it unavailable to legitimate users.
- Brute-Force Attacks: Repeatedly guessing credentials or API keys.
- Data Scraping: Malicious actors rapidly extracting large amounts of data.
- Resource Exhaustion: Preventing a single client from monopolizing server resources.
Implement different rate limits based on user roles, API endpoints, or subscription tiers. Provide clear error messages (e.g., 429 Too Many Requests) when limits are exceeded.
Secure API Design Principles
Security should not be an afterthought but an integral part of the API design process. By embedding security principles into the architecture from the ground up, you build inherently more resilient and trustworthy systems. These API design principles ensure that security is baked in, not bolted on, aligning with the core tenets of robust api security best practices.
1. Principle of Least Privilege
Grant only the minimum permissions necessary for a user or system to perform its function. This applies to both human users and other services interacting with your API. If a microservice only needs to read customer profiles, it should not have write access or access to sensitive financial data. This minimizes the impact of a compromised account or service.
2. Secure Defaults
Design APIs with security as the default. This means:
- Deny by Default: Access should be explicitly granted, not assumed. If a new endpoint is added, it should be inaccessible until permissions are explicitly configured.
- Strong Configurations: Default configurations should prioritize security (e.g., strong password policies, disabled debug modes).
- Minimal Information Exposure: Error messages should not expose internal system details by default.
3. Attack Surface Reduction
Minimize the exposed functionality and data. Every exposed endpoint, parameter, and data field is a potential attack vector.
- Remove Unused Endpoints/Parameters: Regularly audit and remove any API endpoints or parameters that are no longer in use.
- Precise Data Return: Only return the data that the client explicitly requests and needs. Avoid "excessive data exposure."
- Internal vs. External APIs: Clearly segment internal APIs (with less strict external controls) from external APIs (which require robust public-facing security).
4. API Versioning with Security in Mind
As APIs evolve, security flaws may be discovered, or better security practices may emerge. Effective API versioning allows you to introduce security improvements without immediately breaking existing clients. When deprecating older versions that might have known vulnerabilities, ensure a clear communication strategy and migration path for clients to upgrade to more secure versions. This proactive approach to version management is a key aspect of long-term API security health.
Advanced API Security Measures
Beyond the foundational practices, advanced security measures provide additional layers of defense, helping organizations combat sophisticated threats and achieve a higher level of resilience. These measures are often implemented at the infrastructure level or through specialized tools, further solidifying API security best practices.
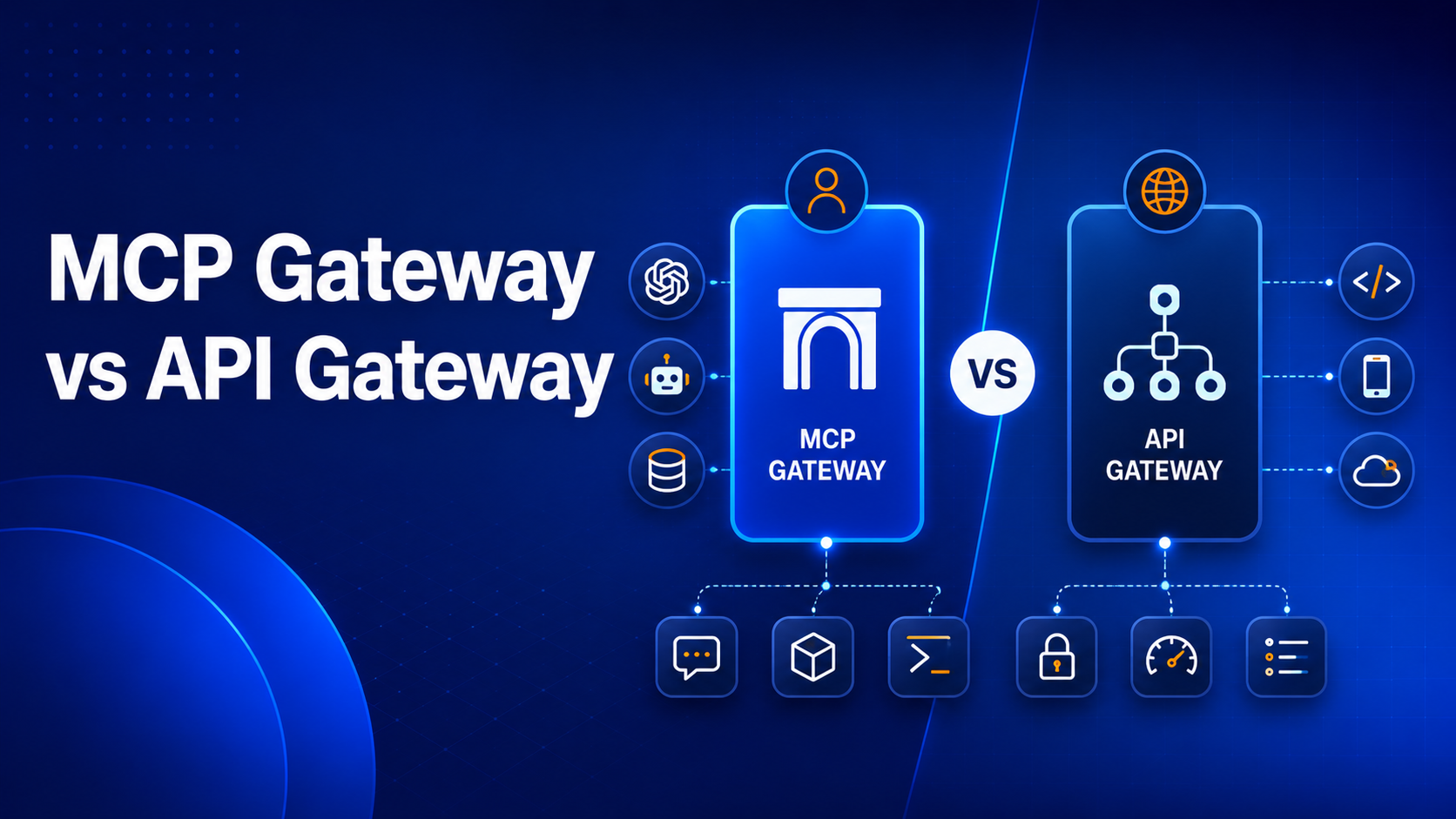
1. API Gateways as a Security Enforcement Point
An API Gateway acts as a single entry point for all API requests, providing a crucial choke point for security enforcement. It can centralize:
- Authentication and Authorization: Offloading these concerns from backend services.
- Rate Limiting and Throttling: Protecting backend APIs from overload and abuse.
- Traffic Filtering: Blocking malicious requests based on IP, headers, or payload content.
- Threat Protection: Applying advanced policies to detect and mitigate common attacks.
- Logging and Monitoring: Providing a central point for capturing API traffic for security analysis.
Leveraging an API gateway security is a cornerstone of modern API security architecture.
2. API Monitoring and Logging
Proactive monitoring and comprehensive logging are indispensable for detecting and responding to security incidents in real time. Implement:
- Centralized Logging: Aggregate all API access logs, error logs, and security event logs into a centralized system for easy analysis.
- Real-Time Monitoring: Use tools to monitor API traffic for anomalies, unusual access patterns, high error rates, or suspected attacks.
- Alerting: Set up automated alerts for critical security events to notify security teams immediately.
- Auditing: Maintain immutable logs for forensic analysis and compliance purposes.
Effective API monitoring provides crucial visibility into the health and security posture of your APIs.
3. API Testing for Security Vulnerabilities
Regular and thorough security testing is essential to uncover vulnerabilities before they can be exploited. Integrate various testing methods into your CI/CD pipeline:
- Static Application Security Testing (SAST): Analyzes source code for security flaws before compilation.
- Dynamic Application Security Testing (DAST): Tests the running application by simulating attacks.
- Interactive Application Security Testing (IAST): Combines SAST and DAST, monitoring application behavior from within.
- Penetration Testing: Ethical hackers simulate real-world attacks to find vulnerabilities.
- Fuzz Testing: Sends malformed or unexpected data to API endpoints to uncover crashes or unexpected behavior.
Understanding what is API testing and utilizing the best API testing tools and platforms are crucial steps.
4. Web Application Firewalls (WAFs)
While API Gateways offer API-specific protections, WAFs provide an additional layer of defense by filtering, monitoring, and blocking HTTP traffic to and from a web application or API. They can protect against common web attacks such as SQL injection, XSS, and broken authentication, often based on signature-based rules and behavioral analysis.
5. Zero Trust Architecture
Adopt a "never trust, always verify" approach. In a Zero Trust model, no user, device, or application is inherently trusted, regardless of whether it is inside or outside the network perimeter. Every request to an API, even from an internal service, must be authenticated and authorized. This drastically reduces the attack surface and minimizes the impact of potential breaches. Implementing Zero Trust for internal APIs is particularly critical in microservices environments.
Organizational and Operational Best Practices
Effective API security extends beyond technical controls; it encompasses organizational processes, policies, and continuous improvement. These operational API security best practices ensure that security is ingrained in the culture and workflows of your development and operations teams.
1. Regular Security Audits and Penetration Testing
Scheduled security audits and penetration tests by independent third parties are essential. These provide an objective assessment of your API's security posture, identifying vulnerabilities that internal teams might overlook. Regular testing ensures that your defenses remain robust against evolving threats and that new features haven't introduced unforeseen weaknesses.
2. Developer Education and Awareness
Developers are the first line of defense. Invest in continuous security training for your development teams. Educate them on secure coding practices, common API vulnerabilities (like the OWASP Top 10), and the specific security policies and tools used within your organization. Foster a culture where security is everyone's responsibility, not just the security team's.
3. Incident Response Plan
Despite all precautions, breaches can happen. A well-defined and regularly practiced incident response plan is critical for minimizing the damage and recovery time from a security incident. This plan should outline:
- Detection and identification of security events.
- Containment strategies to limit the impact of a breach.
- Eradication steps to remove the threat.
- Recovery procedures to restore normal operations.
- Post-incident analysis to learn from the event and improve defenses.
4. API Lifecycle Security
Security considerations must span the entire API lifecycle management, from design and development to deployment, deprecation, and retirement. Integrating security checkpoints at each stage, such as threat modeling during design, security testing during development, and vulnerability scanning before deployment, ensures continuous protection. This holistic view helps to prevent security issues from being introduced at any point in the API's existence.
5. API Access Management
Centralized API access management is crucial for granular control over who can access your APIs and under what conditions. This involves:
- Unified Identity Management: Integrating API access with enterprise identity providers.
- Policy Enforcement: Applying consistent access policies across all APIs.
- Auditing Access: Tracking all access attempts and changes to permissions.
- Revocation Mechanisms: Quickly revoking access for compromised credentials or unauthorized users.
The Role of API Management Platforms in Security
Modern API management platforms are indispensable tools for implementing and enforcing api security best practices at scale. They provide a comprehensive suite of features that centralize security controls, enhance visibility, and automate enforcement across your entire API ecosystem.
- Centralized Security Policies: API management platforms allow you to define and apply API management policies centrally across all your APIs, regardless of their backend implementation. This includes authentication rules, authorization policies, rate limiting, IP whitelisting/blacklisting, and threat protection. Centralized policy management ensures consistency and reduces the chance of misconfiguration on individual APIs.
- Unified Visibility: These platforms offer a single pane of glass for monitoring API traffic, usage patterns, and security events. This unified visibility simplifies the detection of suspicious activities, makes auditing easier, and provides crucial insights into the overall security posture of your API program.
- Automated Enforcement: Policies defined within an API management platform are automatically enforced at the gateway layer. This automation ensures that security controls are consistently applied to every API request, without manual intervention, significantly reducing the operational overhead of security management.
- Developer Portal Security: A well-secured API developer portal is vital, especially when exposing APIs externally. API management platforms ensure developer portal security when exposing APIs externally by handling secure developer onboarding, API key generation, user management, and access control for documentation and sandbox environments. This protects the gateway itself and the underlying APIs from attacks originating from the developer ecosystem.
Key Takeaways for Robust API Security
Securing your APIs is an ongoing journey, not a destination. It demands continuous vigilance, adaptation to new threats, and a proactive mindset. The digital economy runs on APIs, and their integrity is paramount for business continuity and customer trust. By embedding security at every stage – from initial design and development through to deployment and ongoing operations – organizations can build robust, resilient systems capable of withstanding the dynamic threat landscape.
Remember that technology alone is not enough; a strong security culture, continuous education, and a well-practiced incident response plan are equally critical. Embrace these API security best practices, leverage powerful API management tools, and foster a security-first mindset across your organization to safeguard your digital future. Investing in API security today is an investment in your enterprise's long-term stability and success.
FAQs
1. What is the primary difference between API authentication and authorization?
Authentication is the process of verifying who a user or application is (e.g., providing credentials like API keys or tokens). Authorization, which happens after authentication, determines what that authenticated user or application is allowed to do (e.g., access specific resources or perform certain actions). Both are critical components of secure API access management.
2. Why is HTTPS/TLS crucial for API security?
HTTPS/TLS (Transport Layer Security) encrypts all data transmitted between a client and an API server. This prevents eavesdropping (sniffing sensitive data), tampering (altering data in transit), and Man-in-the-Middle attacks (where an attacker intercepts and potentially modifies communication). Without HTTPS, API communication is vulnerable to various forms of interception and compromise.
3. How does an API Gateway enhance API security?
An API Gateway acts as a central enforcement point, allowing organizations to apply consistent API management policies for authentication, authorization, rate limiting, and traffic filtering across all APIs. It offloads these security concerns from backend services, simplifies security management, and provides a unified point for logging and monitoring API traffic, effectively creating a strong perimeter defense.
4. What are some common API security vulnerabilities listed by OWASP?
The OWASP API Security Top 10 highlights critical vulnerabilities such as Broken Object Level Authorization (BOLA), Broken User Authentication, Excessive Data Exposure, Lack of Resources & Rate Limiting, and Security Misconfiguration. These represent the most frequent and impactful weaknesses found in APIs today, making them essential targets for remediation.
5. What role does "Zero Trust" play in modern API security?
Zero Trust is a security model that operates on the principle of "never trust, always verify." For APIs, this means every request, whether from inside or outside the network, must be authenticated, authorized, and continuously validated. It minimizes implicit trust, segmenting networks and enforcing granular access controls, which significantly reduces the attack surface and limits potential damage from a breach, especially for internal APIs.
You’ve spent years battling your API problem. Give us 60 minutes to show you the solution.
.svg)






.avif)
