API Integration
Mastering API Design Patterns for Robust, Scalable APIs
Updated on:
April 21, 2026
TL;DR
1. API design patterns ensure robust, scalable, and maintainable APIs.
2. Resource modeling with clear naming and HTTP methods are foundational patterns.
3. Security, versioning, idempotency, and caching are critical for reliability and performance.
4. HATEOAS embodies true REST for evolvability and reduced coupling.
5. Prioritizing developer experience through documentation and consistency drives adoption.
Current digital ecosystems thrive on seamless interconnections, powered by APIs that serve as the backbone for modern applications. Yet, merely exposing data isn't enough; the architecture underlying these interfaces critically determines their long-term viability. Crafting APIs that stand the test of time, scale effortlessly, and remain robust against evolving demands requires a deliberate approach—one rooted in established API design patterns.
These aren't just theoretical constructs; they are proven blueprints for solving common challenges in API development, ensuring consistency, predictability, and a superior developer experience. By embracing these patterns, we move beyond basic functionality to engineer APIs that are truly foundational assets, capable of driving innovation and sustaining growth in dynamic environments.
What are API Design Patterns and Why Are They Essential?
At its heart, an API design pattern is a reusable solution to a commonly occurring problem in API architecture. It’s not a finished design that can be directly implemented, but rather a template for how to solve a particular design issue in a consistent and effective way. Just as software engineering uses design patterns to build robust applications, API development benefits immensely from these established blueprints to ensure interfaces are not only functional but also intuitive, secure, and performant.
The importance of mastering these patterns cannot be overstated. In a landscape where APIs are the primary mode of digital interaction, their quality directly impacts user adoption, integration speed, and overall system stability. Well-applied API design patterns lead to:
- Robustness: Patterns help anticipate and mitigate common issues like error handling, data consistency, and security vulnerabilities, making APIs more resilient.
- Scalability: Designs that incorporate caching, statelessness, and efficient resource management can handle increasing loads without significant performance degradation.
- Maintainability: Consistent application of patterns across an API makes it easier for developers to understand, debug, and extend, reducing technical debt.
- Consistency: By following established patterns, APIs become predictable, reducing the learning curve for new developers and fostering faster integration.
- Developer Experience (DX): An API built with good design patterns is often more intuitive, better documented (implicitly through its structure), and a pleasure to work with, directly impacting its adoption.
Ignoring these patterns often results in "API sprawl"—a disorganized collection of inconsistent, hard-to-maintain, and insecure interfaces that hinder innovation rather than accelerate it. Therefore, understanding and applying these fundamental API design patterns is not merely a best practice; it is a critical skill for any developer or architect aiming to build successful digital products.
Foundational Design Patterns: Resource-Oriented Architecture
The most pervasive and foundational API design pattern is the Resource-Oriented Architecture (ROA), best exemplified by RESTful APIs. REST (Representational State Transfer) is an architectural style that defines a set of constraints for designing networked applications. It treats everything as a "resource," identified by a unique URI, which clients can interact with using a uniform interface.
The core tenets of ROA, derived from REST, are crucial design patterns in themselves:
- Client-Server Separation: This pattern mandates a clear distinction between the client (which handles the user interface and user state) and the server (which manages data and business logic). This separation allows both components to evolve independently, enhancing scalability and portability.
- Statelessness: A key REST constraint and a powerful design pattern. Each request from the client to the server must contain all the information needed to understand and process the request. The server should not store any client context between requests. This simplifies server design, improves reliability against partial failures, and significantly enhances scalability by allowing any server to handle any request.
- Uniform Interface: This is perhaps the most defining pattern of REST. It simplifies the overall system architecture by providing a single, consistent way for components to interact. This includes:
- Resource Identification: Resources are identified by URIs (e.g., `/users/123`).
- Resource Manipulation Through Representations: Clients manipulate resources by sending representations (e.g., JSON, XML) to the server.
- Self-Descriptive Messages: Each message includes enough information (e.g., HTTP headers, status codes) to describe how to process it.
- Cacheability: Responses from the server must explicitly or implicitly label themselves as cacheable or non-cacheable. This allows clients and intermediaries (proxies) to cache responses, significantly reducing server load and network latency for repeated requests.
These architectural patterns form the bedrock of robust and scalable API design, fostering loose coupling and leveraging the inherent strengths of the web's infrastructure. When considering alternatives like SOAP, REST's emphasis on these patterns makes it generally more lightweight and adaptable for modern web services.
Pattern for Clarity: Effective Resource Modeling
Beyond the architectural style, how you actually define and name your resources is a crucial design pattern for clarity and intuitiveness. Effective resource modeling makes an API self-documenting and easy to grasp for consuming developers. The goal is to represent business entities and their relationships logically.
Key principles for resource modeling as a design pattern:
- Use Nouns, Not Verbs, in URLs: This is a cardinal rule. Resources are "things," not "actions." The HTTP methods (GET, POST, PUT, DELETE) convey the action. Instead of `/getAllUsers` or `/updateProduct`, use `/users` and `/products`. This separates concerns and makes URLs more stable.
- Use Plural Nouns for Collections: Consistently use plural nouns for collections of resources (e.g., `/users`, `/orders`, `/products`). A specific resource within a collection is then identified by its unique ID (e.g., `/users/{id}`).
- Nest Resources Logically for Relationships: When a resource is conceptually owned by or related to another, represent this hierarchy in the URL path. For example, to get all orders for a specific user, use `/users/{user_id}/orders`. This pattern creates an intuitive navigation path.
- Keep URLs Clean, Simple, and Predictable: Avoid overly long, complex, or redundant URL paths. URLs should be easy to read, type, and remember. They should also be "hackable," meaning a developer can intuitively modify parts of the URL to explore related resources (e.g., changing `/users/123/orders` to `/users/123` to get user details).
- Maintain Consistent Casing: Choose a single casing convention (e.g., kebab-case for URL segments: `user-accounts`) and apply it uniformly across all resource paths.
- Avoid File Extensions in URLs: Do not include `.json`, `.xml`, or other format specifiers in the URL. Use the HTTP `Accept` header to indicate the desired response format, which is a more flexible and RESTful approach.
By adhering to these patterns, your API's resource structure becomes a predictable map that developers can navigate with ease, significantly improving the learning curve and reducing integration time.
Pattern for Action: Mastering HTTP Methods
The intelligent use of HTTP methods (verbs) is a fundamental API design pattern that explicitly defines the intended action on a resource. Each method carries a specific semantic meaning, and adhering to these semantics is crucial for building predictable, cacheable, and robust APIs.
Here’s how to master the primary HTTP methods:
- GET (Retrieve): Used to fetch a representation of a resource or a collection of resources. GET requests must be safe (meaning they don't alter the server's state) and idempotent (multiple identical requests yield the same result as a single one). For example, `GET /products` retrieves all products, and `GET /products/{id}` retrieves a specific product.
- POST (Create): Primarily used to create new resources. POST requests are generally not idempotent, as sending the same POST request multiple times could create multiple identical resources. For instance, `POST /users` creates a new user, with the data supplied in the request body.
- PUT (Update/Replace): Used to update an existing resource or create one if it doesn't exist. PUT requests are idempotent; repeatedly sending the same PUT request will result in the same resource state. `PUT /users/{id}` replaces the entire resource at `{id}` with the provided data.
- PATCH (Partial Update): Designed for applying partial modifications to a resource. Unlike PUT, PATCH only sends the specific changes, not the entire resource representation. PATCH requests are also idempotent, although their implementation can be more complex to ensure this property. Example: `PATCH /users/{id}` to update only a user's email address.
- DELETE (Remove): Used to remove a specific resource. DELETE requests are idempotent; deleting a resource multiple times has the same ultimate effect (the resource remains removed). Example: `DELETE /products/{id}` removes a product.
Misusing these HTTP methods (e.g., using GET to change data or POST to update an existing resource when PUT is more appropriate) leads to an API that is confusing, violates cacheability rules, and can introduce unexpected side effects. Proper method usage is a powerful design pattern for creating clear, predictable, and maintainable API interactions.
Pattern for Communication: Leveraging HTTP Status Codes
HTTP status codes are a critical communication design pattern in RESTful APIs, acting as the primary means for the server to inform the client about the outcome of a request. Using them accurately and consistently is vital for robust error handling and client-side logic. They fall into five broad categories:
- 1xx Informational Responses: (e.g., 100 Continue) Rarely used in typical API responses, as they indicate an interim state.
- 2xx Success Responses: Indicate that the client's request was successfully received, understood, and accepted.
- `200 OK`: The request succeeded. This is the most common success code.
- `201 Created`: A new resource was successfully created as a result of the request (typically POST). The response body should contain the representation of the new resource and a `Location` header pointing to its URI.
- `204 No Content`: The request succeeded, but there is no content to send back in the response body (e.g., a successful DELETE operation or a PUT that updates without returning a resource).
- `202 Accepted`: The request has been accepted for processing, but the processing has not been completed (e.g., for asynchronous operations).
- 3xx Redirection Messages: Inform the client that further action needs to be taken to complete the request. Less common for direct API interactions, but sometimes used for permanent resource moves (`301 Moved Permanently`).
- 4xx Client Error Responses: Indicate that the client made a mistake or provided invalid input. These errors should be fixable by the client.
- `400 Bad Request`: The server cannot process the request due to malformed syntax, invalid request parameters, or other client-side errors not covered by more specific 4xx codes.
- `401 Unauthorized`: The client needs to authenticate to get the requested response.
- `403 Forbidden`: The client has authenticated but does not have the necessary permissions to access the resource or perform the action.
- `404 Not Found`: The server cannot find the requested resource.
- `405 Method Not Allowed`: The HTTP method used in the request is not supported for the requested resource (e.g., trying to POST to a read-only resource).
- `409 Conflict`: The request conflicts with the current state of the resource (e.g., trying to create a resource that already exists).
- `429 Too Many Requests`: The user has sent too many requests in a given amount of time (rate limiting).
- 5xx Server Error Responses: Indicate that the server failed to fulfill a request due to an issue on the server's side. These errors are typically unrecoverable by the client without server-side fixes.
- `500 Internal Server Error`: A generic error message, given when an unexpected condition was encountered.
- `503 Service Unavailable`: The server is not ready to handle the request (e.g., overloaded or down for maintenance).
Beyond just the status code, always provide a clear, machine-readable error message in the response body for 4xx and 5xx errors, explaining what went wrong and how the client can potentially resolve the issue (for client errors) or what to expect (for server errors).
Pattern for Evolution: Consistent API Versioning
An API versioning strategy is an essential design pattern for managing the evolution of your API over time without breaking existing client integrations. As APIs mature, new features are added, old ones are deprecated, and breaking changes inevitably occur. Without a clear versioning strategy, these changes can lead to chaos, forcing all clients to update simultaneously and causing significant disruption.
The importance of consistent versioning includes:
- Backward Compatibility: Versioning allows you to introduce new features or improvements without immediately forcing all existing clients to adapt. Older clients can continue to operate against an older, stable version, while new clients can adopt the latest functionalities.
- Graceful Evolution: APIs are living systems. Versioning provides a structured way to manage changes, offering a clear roadmap for how the API will evolve and providing a grace period for developers to migrate.
- Developer Trust: A clear commitment to versioning demonstrates reliability and stability. Developers are more confident integrating with an API when they know their applications won't suddenly break due to unforeseen changes.
- Managed Deprecation: When functionality needs to be removed or drastically altered, versioning allows for a smooth deprecation process. You can communicate clearly that an older version will be sunsetted, giving clients ample time and guidance to migrate to a newer version.
Common REST versioning strategies as design patterns include:
- URI Path Versioning (e.g., `/v1/users`, `/v2/users`): This is the most common and often preferred method because it makes the version explicit and discoverable directly in the URL. It's clear and simple to implement.
- Custom Header Versioning (e.g., `X-Api-Version: 1`): Keeps URLs cleaner by placing the version in an HTTP header. However, it can be less discoverable as the version isn't visible in the URL itself.
- Media Type Versioning (e.g., `Accept: application/vnd.myapi.v1+json`): Considered the most RESTful approach, as it leverages content negotiation. It's highly flexible but can be more complex for clients to implement.
- Query Parameter Versioning (e.g., `/users?version=1`): Simpler to implement than media type versioning, but less RESTful as query parameters are generally for filtering or pagination, not identifying a specific resource version.
Regardless of the chosen strategy, consistency across your API and clear communication about version updates and deprecation policies are paramount for a successful API lifecycle.
Pattern for Trust: Robust Security Measures
Security is not merely a feature; it's an inherent API design pattern that must be woven into every layer of your API. A breach in API security can lead to devastating consequences, including data loss, service interruptions, and severe reputational damage. Building robust security requires a multi-faceted approach:
- Authentication: This pattern verifies the identity of the client making the request. Without proper authentication, any client could potentially access your API. Common authentication mechanisms include:
- OAuth 2.0: An industry-standard protocol for delegated authorization, allowing third-party applications to access user resources without exposing credentials.
- API Keys: Simple tokens for identifying and authenticating client applications, often used for public APIs with rate limits.
- JWT (JSON Web Tokens): A compact, URL-safe means of representing claims to be transferred between two parties. Often used in conjunction with OAuth or as a direct authentication token.
- Authorization: After a client is authenticated, this pattern determines whether the client has the necessary permissions to perform the requested action on a specific resource. Implement Role-Based Access Control (RBAC) or Attribute-Based Access Control (ABAC) to enforce granular permissions.
- Use HTTPS/TLS: Always enforce the use of HTTPS (HTTP over TLS/SSL) for all API communication. This encrypts data in transit, preventing eavesdropping and Man-in-the-Middle attacks.
- Input Validation and Sanitization: A critical pattern to prevent injection attacks (e.g., SQL injection, XSS) and other data-related vulnerabilities. Validate all input from clients against expected formats, types, and constraints. Sanitize inputs to remove potentially malicious characters or scripts.
- Rate Limiting and Throttling: Implement limits on the number of requests a client can make within a given timeframe. This pattern protects your API from abuse, brute-force attacks, and Denial-of-Service (DoS) attacks, contributing to overall stability and availability. For more details, refer to rate limiting strategies.
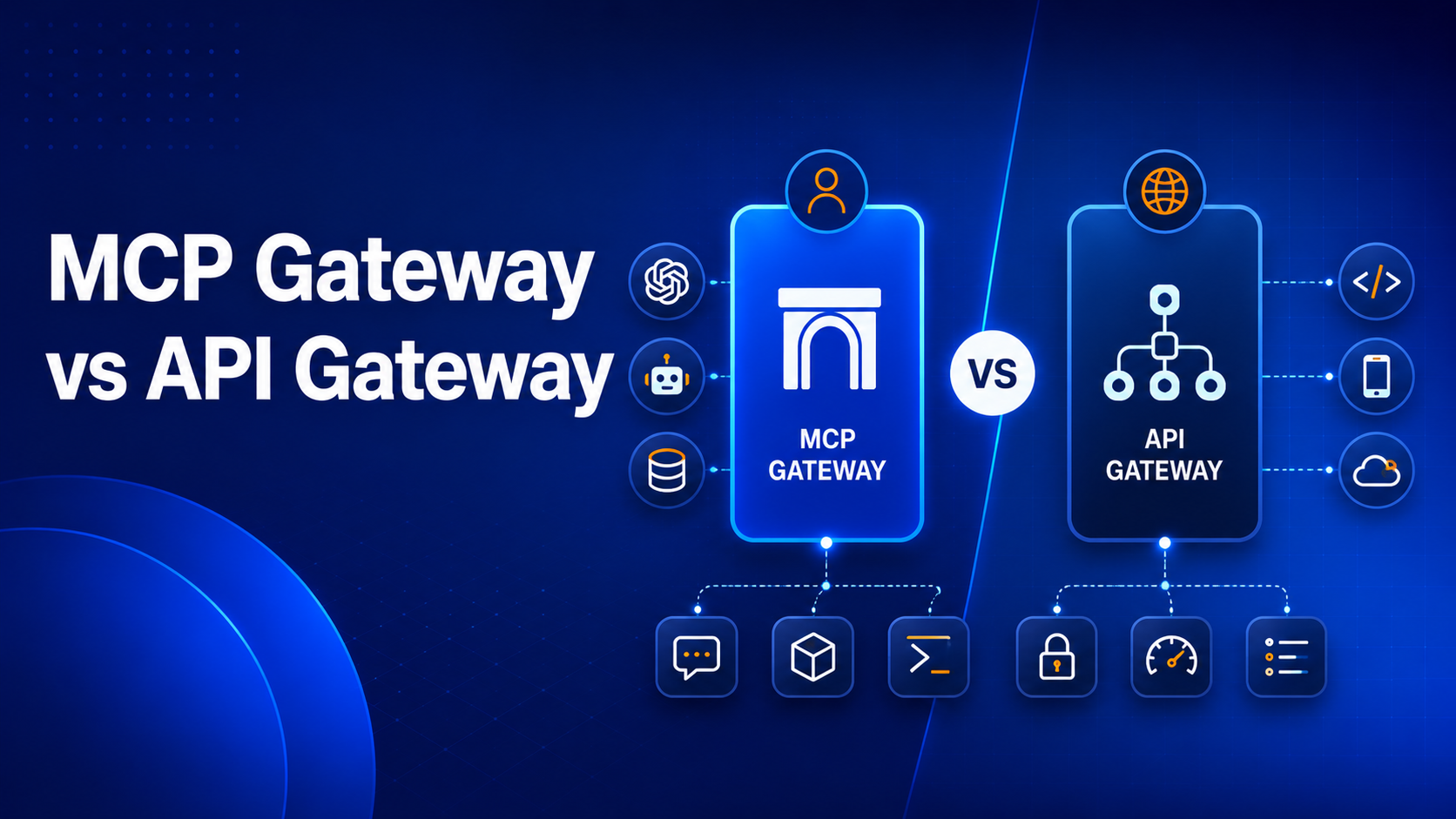
- Secure API Gateways: Employing an API gateway security is a robust pattern for centralizing security policies, handling authentication and authorization, enforcing rate limits, and managing traffic before requests reach your backend services.
- Logging and Monitoring: Implement comprehensive logging for all API requests, responses, and security events. Monitor for suspicious activity, failed authentication attempts, and errors to detect and respond to security incidents promptly.
- Protect Against Common Vulnerabilities: Regularly audit and review your API against industry standards like the OWASP Top 10 for APIs to identify and mitigate known security risks.
By systematically layering these security patterns, you build a resilient API that protects both your data and your users, fostering trust and enabling secure digital interactions.
Pattern for Discoverability: HATEOAS
HATEOAS, or Hypermedia as the Engine of Application State, is a sophisticated and often misunderstood design pattern that represents the highest level of REST maturity (Level 3 on the Richardson Maturity Model). It’s the pattern that truly makes an API self-discoverable and evolvable, akin to how a human navigates the web by clicking links rather than memorizing URLs.
At its core, the HATEOAS pattern dictates that API responses should not only contain data but also include links to related resources and available actions that the client can perform next. Instead of clients having prior, hardcoded knowledge of how to construct URLs for various operations, they navigate the API solely by following the hypermedia links provided within the responses.
For example, a `GET /users/{id}` response for a user resource might include:
{
"id": "123",
"name": "Jane Doe",
"email": "jane.doe@example.com",
"_links": {
"self": { "href": "/users/123" },
"orders": { "href": "/users/123/orders" },
"update_profile": { "href": "/users/123", "method": "PUT" },
"delete_user": { "href": "/users/123", "method": "DELETE" }
}
}
This provides immediate information about what actions are available and where to go next, based on the current state of the resource.
The benefits of implementing HATEOAS as a design pattern include:
- Reduced Coupling: Clients are less coupled to the server's specific URI structure. If a URI changes, as long as the link relation is preserved, clients can continue to function without requiring code modifications.
- Enhanced Evolvability: The API can evolve more gracefully. New features or workflows can be introduced by simply adding new links to responses. Older links can be removed without breaking existing clients who don't expect them.
- True Discoverability: Developers and even automated agents can discover available actions and navigate the API by inspecting the response, making the API truly dynamic and self-descriptive.
While implementing HATEOAS adds initial complexity, it significantly enhances the flexibility, resilience, and longevity of an API by moving beyond simple data exposure to enable a more flexible and evolvable client-server interaction model, making it truly adaptable to change.
Pattern for Reliability: Ensuring Idempotency
Idempotency is a crucial design pattern that ensures reliability and predictability in API interactions, particularly in distributed systems where network failures, timeouts, and retries are commonplace. An operation is idempotent if executing it multiple times produces the same result as executing it once, without any unintended side effects.
Consider scenarios where idempotency is vital:
- Network Interruptions: A client sends a request (e.g., to create an order) but doesn't receive a response due to a network timeout. Unsure if the request succeeded, the client might retry. Without idempotency, this could lead to duplicate orders.
- Client-Side Retries: Many client libraries automatically retry failed requests. If these retries trigger non-idempotent actions, unintended consequences (like multiple charges for a single payment) can occur.
HTTP methods inherently support idempotency in different ways:
- Naturally Idempotent:
- `GET`: Always retrieves the same resource state.
- `PUT`: Even if sent multiple times, it replaces the resource with the same data, resulting in the same final state.
- `DELETE`: If sent multiple times, it ensures the resource is removed (or remains removed), yielding the same outcome.
- Not Naturally Idempotent:
- `POST`: Typically used to create new resources. Sending the same POST request multiple times will usually create multiple resources.
To make a `POST` operation effectively idempotent, a common design pattern involves using an "idempotency key" or a "transaction ID" provided by the client in the request header. The server stores this unique key and checks if a request with that key has already been processed. If it has, the server returns the original response from the first successful processing without re-executing the operation, thus preventing duplicate actions.
Example with an Idempotency Key:
POST /orders
Idempotency-Key: a1b2c3d4e5f6g7h8
Content-Type: application/json
{
"item_id": "product123",
"quantity": 2
}
If the server receives this request multiple times with the same `Idempotency-Key`, it processes the order only once and returns the same `201 Created` response for subsequent identical requests. Ensuring idempotency is a powerful way to design APIs that are robust against transient errors, can be safely retried, and maintain data integrity, which is essential for mission-critical applications.
Pattern for Performance: Optimizing with Caching Strategies
Optimizing API performance and ensuring scalability are critical concerns for any successful digital product. Caching is a powerful design pattern that significantly reduces server load, decreases latency, and improves the overall responsiveness of your API. Leveraging HTTP caching mechanisms is a cornerstone of this optimization strategy:
- HTTP Caching Headers: These are the most direct way to enable caching at various layers (client, proxy, CDN).
- `Cache-Control`: A general-purpose header that directs caching mechanisms. It specifies if a resource is cacheable, for how long, and by whom. Directives like `public`, `private`, `no-cache`, `max-age={seconds}`, and `no-store` offer fine-grained control.
- `ETag` (Entity Tag): A unique identifier for a specific version of a resource. When a client requests a resource for the first time, the server returns the `ETag` in the response header. For subsequent requests, the client can send an `If-None-Match` header with the cached ETag. If the resource hasn't changed, the server responds with a `304 Not Modified` status, saving bandwidth by not sending the entire response body.
- `Last-Modified`: Indicates the last time a resource was modified. Similar to `ETag`, clients can use `If-Modified-Since` in subsequent requests. If the resource hasn't been updated since that time, the server returns `304 Not Modified`.
- Client-Side Caching: Web browsers and client applications can store API responses locally based on `Cache-Control` and other HTTP headers. This reduces the need to make network requests for data that hasn't changed.
- Proxy/CDN Caching: Content Delivery Networks (CDNs) and intermediary proxies can cache API responses geographically closer to the user. This significantly reduces latency for distributed client bases and offloads traffic from your origin servers.
- Server-Side Caching: Implement caching layers within your API infrastructure (e.g., Redis, Memcached, database query caches) to store frequently accessed data or computationally expensive results. This reduces database hits and processing time for common requests.
- Rate Limiting: While not strictly a caching mechanism, implementing rate limiting protects your backend resources from being overwhelmed by excessive requests from individual clients, contributing to overall stability and availability.
- Pagination and Filtering: For large collections of data, implement pagination (e.g., `?page=1&size=10`) and filtering (e.g., `?status=active`). This pattern allows clients to request only the precise subset of data they need, reducing payload size and server-side processing.
- Minimize Payload Size: Design responses to return only necessary data. Use efficient data formats (like JSON) and enable compression (e.g., Gzip) to minimize the amount of data transferred over the network.
By strategically combining these caching patterns, you can build a highly performant and scalable API capable of handling significant loads efficiently, providing a faster and more responsive experience for consumers.
Pattern for Adoption: Designing for Developer Experience (DX)
A technically robust API is only truly successful if developers find it easy and enjoyable to use. Prioritizing Developer Experience (DX) is a critical design pattern that transforms an API from a mere interface into a powerful tool that fosters adoption, innovation, and a vibrant ecosystem. An intuitive API with excellent DX significantly reduces the time-to-first-call and accelerates integration. Here’s how to design for optimal DX and practicality:
- Comprehensive and Accurate API Documentation: This is arguably the single most important element of good DX. Use tools like OpenAPI/Swagger to generate interactive, up-to-date documentation. Include clear examples for requests and responses, detailed schemas, all authentication details, error codes, and common use cases. Good API documentation acts as the primary interface for developers and dictates how quickly they can onboard.
- Consistent Design Across All Endpoints: Apply uniform naming conventions (resources, parameters, fields), data structures, and error handling patterns throughout your entire API. Inconsistency breeds confusion, increases the learning curve, and slows down development.
- Predictable Behavior: Developers expect APIs to behave predictably. Avoid hidden side effects, inconsistent response formats, or arbitrary rate limits that change without notice. Clear communication about any potential changes is key.
- Meaningful Error Messages: Beyond just returning appropriate HTTP status codes, provide clear, actionable error messages in the response body. Explain *what* went wrong (e.g., "Invalid email format") and *how* to fix it (e.g., "Please provide a valid email address").
- Sandbox Environments: Offer a dedicated sandbox environment where developers can test their integrations without affecting live production data or incurring real-world charges. This pattern speeds up development, allows for safe experimentation, and reduces integration risk.
- SDKs and Client Libraries (Optional but Recommended): For popular programming languages, providing official Software Development Kits (SDKs) or client libraries can significantly reduce the effort required for integration, abstracting away the complexities of HTTP requests and JSON parsing.
- Self-Service Developer Portal: A developer portal that offers a single point of entry for documentation, API keys, usage analytics, support resources, and community forums empowers developers to help themselves and dramatically accelerates onboarding.
- Clear Communication Channels: Make it easy for developers to ask questions, report bugs, provide feedback, and stay informed about updates, whether through a dedicated support channel, community forum, or a public changelog.
Ultimately, designing for developer experience means empathizing with the consumer of your API. An API that is intuitive, well-documented, well-supported, and consistent will be adopted faster and lead to greater innovation within your ecosystem.
What Are the Common Pitfalls to Avoid in RESTful API Design?
Even with a good understanding of API design patterns, developers can fall into common traps that undermine the robustness, scalability, and maintainability of their APIs. Recognizing these anti-patterns is as important as knowing the good patterns:
- Using Verbs in URLs (The Action-Oriented Anti-Pattern): This is a classic violation of the resource-oriented principle. URLs should represent nouns (resources), not verbs (actions). Avoid `/getUsers`, `/createUser`, or `/deleteOrder`. Instead, use `/users` with GET, POST, or DELETE methods respectively.
- Ignoring HTTP Methods (The "Everything is POST" Anti-Pattern): Using only POST for all operations, or worse, using GET for state-changing actions, violates REST principles. It leads to confusion, breaks caching mechanisms, makes the API less explicit, and obscures the true intent of the request.
- Lack of Consistent Error Handling: Returning inconsistent HTTP status codes or vague error messages makes debugging a nightmare for client developers. Always provide clear, machine-readable status codes and informative error bodies that explain what went wrong and how to fix it.
- No Versioning Strategy: Launching an API without a clear plan for evolution (no versioning at all) will inevitably lead to breaking changes for existing clients when updates are introduced, causing frustration and distrust.
- Chatty APIs: Requiring clients to make many small, sequential requests to complete a single logical operation (e.g., fetching a user, then a separate call for their address, then individual calls for each of their orders) significantly increases latency and network overhead. Design endpoints that provide aggregated data where appropriate.
- Over-fetching or Under-fetching Data: Returning too much data (e.g., all user details when only a name is needed) wastes bandwidth and processing power. Conversely, returning too little data (requiring multiple calls) leads to chatty APIs. Offer options for field selection, embedded resources, or GraphQL for more efficient data retrieval.
- Poor or Outdated Documentation: The best-designed API in the world is useless if developers can't understand how to use it. If documentation is inaccurate, incomplete, or hard to find, developers will struggle to integrate and adopt your API.
- Neglecting Security: Treating API security as an afterthought leads to critical vulnerabilities. Authentication, authorization, input validation, and secure communication (HTTPS) must be fundamental from the design phase, not bolted on later.
- Stateful APIs (Violating Statelessness): Violating REST's statelessness constraint by storing client session information on the server significantly reduces scalability, reliability, and visibility. Each request should be self-contained and independently understandable.
- Ignoring API Lifecycle Management: Not planning for the full lifecycle—from design and development to deprecation and retirement—means APIs often become technical debt rather than valuable assets.
Awareness of these common pitfalls can guide developers towards more robust, developer-friendly, and sustainable API designs, saving significant time and effort in the long run.
Is Strict Adherence to REST's Constraints Always the Best Path for Your Project?
While the architectural constraints of REST provide an excellent framework for building scalable and maintainable APIs, strict adherence to every single constraint, especially HATEOAS, isn't always the most pragmatic or necessary approach for every project. This brings us to the concept of the Richardson Maturity Model, which describes different levels of RESTfulness:
- Level 0: The Swamp of POX (Plain Old XML/JSON): A single URI, a single HTTP method (often POST), and an XML/JSON payload that describes the action to be performed. Little to no adherence to REST principles.
- Level 1: Resources: Introduces the concept of resources, with separate URIs for different entities, but still often uses a single HTTP method (usually POST) for all interactions.
- Level 2: HTTP Verbs: Utilizes HTTP methods (GET, POST, PUT, DELETE) correctly for intentful actions on resources, along with proper status codes. This is where most "RESTful" APIs operate and achieve most of the benefits of REST, such as clear resource modeling, statelessness, and cacheability.
- Level 3: Hypermedia Controls (HATEOAS): The highest level, where clients navigate the API entirely through hypermedia links provided in responses, making the API truly self-discoverable.
For many projects, operating at Level 2 (using resources and HTTP verbs correctly) is perfectly sufficient and provides most of the benefits of REST. Implementing HATEOAS (Level 3) adds significant complexity, both on the server-side (generating and managing links) and on the client-side (parsing links and dynamically discovering actions). While it offers superior evolvability and reduced coupling, the overhead might not be justified for:
- Simple CRUD APIs where client-side logic is tightly coupled to resource structure anyway (e.g., internal APIs where client and server teams are closely aligned).
- Internal APIs with limited client diversity and high control over client updates, where the cost of dynamic discovery outweighs the benefit.
- Projects with tight deadlines or limited team experience in HATEOAS implementation, where pragmatic delivery is prioritized.
The key is pragmatism. Strive for consistency, clarity, and the benefits that best serve your project's needs. While understanding all REST constraints is vital for a comprehensive grasp of API design patterns, choosing where to draw the line between "pure REST" and "pragmatic REST" is a critical design decision. Often, a "REST-like" API at Level 2, combined with excellent documentation and clear versioning, delivers immense value without the additional complexity of full HATEOAS implementation. The goal is to build robust, scalable, and maintainable APIs, and sometimes that means a practical application of patterns rather than rigid adherence.
FAQs
1. What is the primary difference between REST and SOAP?
REST is an architectural style that typically leverages standard HTTP methods, is resource-oriented, stateless, and supports various data formats like JSON or XML. SOAP, on the other hand, is a protocol that relies heavily on XML for message formatting, is message-oriented with a formal contract (WSDL), and can be stateful. REST is generally favored for its simplicity, flexibility, and performance, making it a better fit for modern web services.
2. Is a RESTful API always stateless, and what does that truly mean?
Yes, statelessness is a core principle and design pattern of REST. It truly means that each request from a client to a server must contain all the information needed to understand and process that specific request. The server should not store any client context, session data, or previous request information between requests. This design choice improves scalability, reliability, and visibility by simplifying server logic and allowing requests to be handled by any available server without dependency on past interactions.
3. Why is HATEOAS considered the "cherry on top" for true RESTful APIs?
HATEOAS (Hypermedia as the Engine of Application State) is considered the "cherry on top" because it enables true self-discoverability and evolvability, reaching the highest level of REST maturity. Instead of clients hardcoding URLs, API responses include hypermedia links to related resources and available actions. This dramatically reduces client-server coupling, allowing the API to evolve without breaking existing clients, which is a powerful aspect of truly flexible distributed systems.
4. How do I choose the right HTTP status codes for my API's responses?
Choose HTTP status codes that accurately reflect the outcome of the request. Use 2xx codes for success (e.g., 200 OK, 201 Created), 4xx codes for client-side errors (e.g., 400 Bad Request, 404 Not Found, 401 Unauthorized), and 5xx codes for server-side errors (e.g., 500 Internal Server Error). Always provide a clear, machine-readable message in the response body for 4xx and 5xx errors to aid debugging and provide actionable insights.
5. What are the most common security concerns when designing a RESTful API?
The most common security concerns include ensuring proper authentication and authorization, protecting against injection attacks (e.g., SQL, XSS), preventing data exposure of sensitive information, implementing robust rate limiting to thwart DoS attacks, safeguarding against broken access control, and mitigating vulnerabilities outlined in the OWASP Top 10. Using HTTPS/TLS for all communications and validating all client input are fundamental safeguards for robust API security.
You’ve spent years battling your API problem. Give us 60 minutes to show you the solution.
.svg)






.avif)
