API Gateway
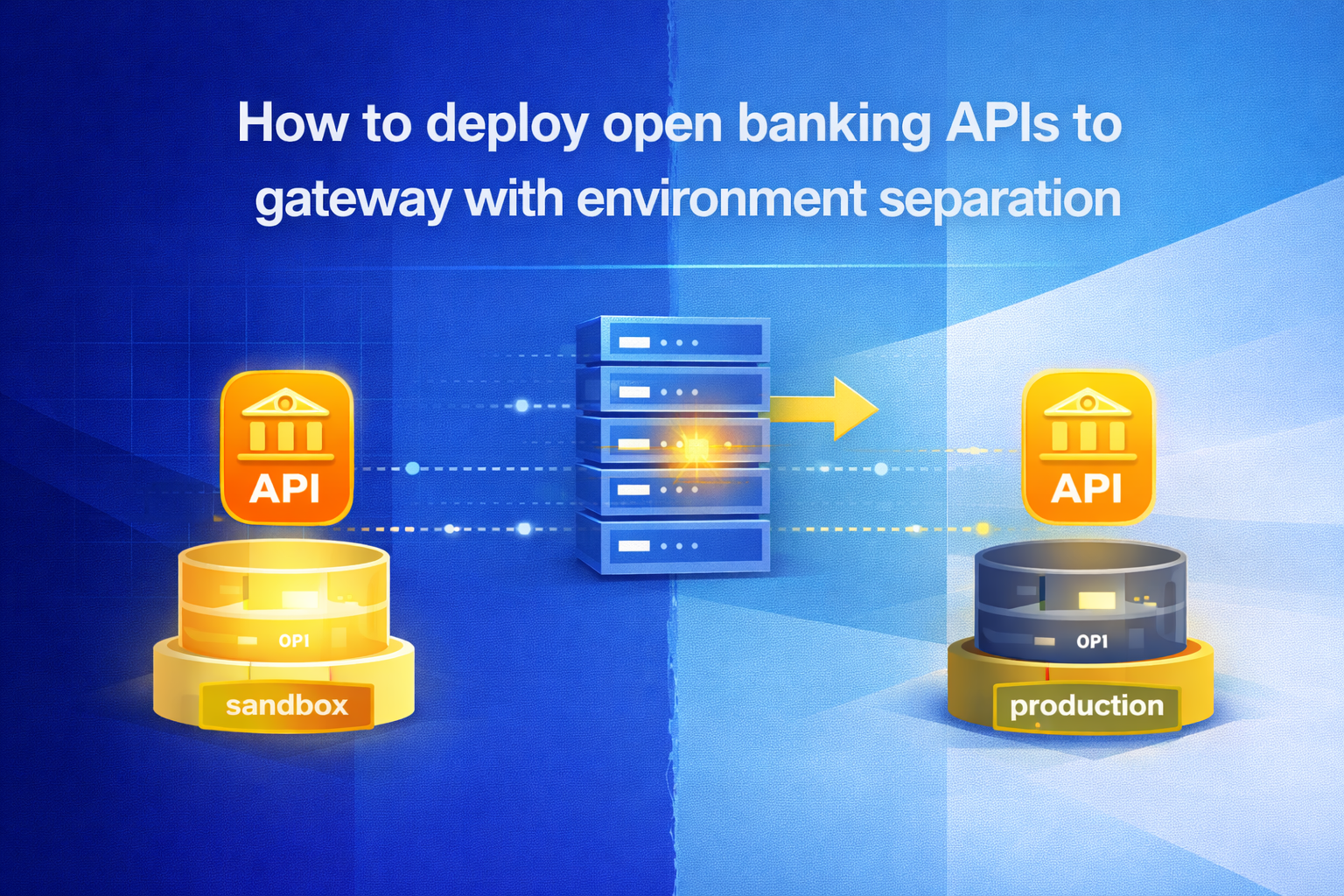
How to deploy open banking APIs to gateway with environment separation
Updated on:
April 21, 2026
TLDR
1. Open banking API deployments require independent gateway configurations, credentials, and policies for dev, stage, and prod.
2. Sharing any configuration layer across environments introduces compliance and data exposure risk.
3. CI/CD pipelines must enforce environment boundaries automatically rather than relying on manual controls.
4. Configuration drift from staging to production is the most common root cause of compliance failures in open banking deployments.
Deploy open banking APIs without environment risk. Book a demo
Open banking APIs carry regulatory obligations that most internal APIs do not. A misconfigured gateway policy, a leaked credential, or a rate limit that was never updated from staging can create compliance exposure that surfaces during audits rather than during development. Environment separation is not an optional engineering practice. It is a structural requirement for any bank or financial institution deploying APIs under PSD2, FAPI, or regional open banking frameworks.
What environment separation means for open banking APIs
Environment separation is the practice of maintaining physically and logically distinct gateway configurations for development, staging, and production so that no credential, policy, or data path crosses between environments without deliberate promotion. For open banking APIs, this means more than separate base URLs. It requires independent gateway instances, isolated identity scopes, distinct policy sets, and controlled promotion workflows that prevent accidental configuration bleed.
The consequences of incomplete separation are significant in regulated environments. A policy tested in staging may not reflect the restrictions enforced in production. A credential created for developer testing may persist into a live environment. Data used to simulate transactions during integration testing may inadvertently connect to real account records. In organizations managing open banking security obligations at scale, these are operational realities rather than theoretical risks.
Open banking API environment roles: dev, stage, and prod
Open banking deployments require three distinct gateway environments, each with a clearly defined purpose and boundary. Teams that treat environments as identical configurations with different domain names will encounter environments bleed the moment release pressure compresses testing timelines.
Development environment: open banking API integration and testing
The development environment is where integration teams build and test against open banking API contracts without touching live data. The gateway configuration here should support rapid iteration, which means higher rate limits, verbose logging, and synthetic or mocked responses. Credentials issued in development must be scoped to this environment only and must never authenticate against staging or production endpoints.
Teams building against accounts, balances, and transaction endpoints should use the open banking API sandbox layer to simulate realistic response patterns. This ensures that edge cases, including consent expiration, insufficient funds, and reversed transactions, are caught before they reach compliance-sensitive pipeline stages.
Staging environment: pre-production compliance validation
Staging bridges development and production. It applies near-production policies including authentication requirements, rate limits, consent enforcement, and schema validation rules. This environment catches configuration gaps that the permissive development setup misses. Contract tests, security scans, and regulatory alignment checks should run automatically against the staging API gateway before any promotion is approved.
The staging gateway configuration should mirror production as closely as possible. Any deviation between staging and production policies creates the risk that a passing staging deployment will behave differently once promoted. This is precisely the category of error that generates compliance incidents in regulated deployments. Teams should treat staging as the final validation checkpoint before production, not an intermediate step.
Production environment: live traffic and regulatory controls
The production environment serves live consumer traffic under strict SLA, consent, and compliance obligations. The gateway enforces real-time token validation, consent scope checks, rate limiting, and audit logging. Policy drift from staging must be blocked by the deployment pipeline rather than identified manually after promotion.
Production credentials must be managed in a secret vault with strict access controls aligned with broader API security practices. No developer should have unreviewed write access to production gateway configurations. Changes must follow approval workflows that create an auditable record consistent with the traceability requirements regulators expect during PSD2 reviews and third-party assessments.
API gateway configuration checklist for dev, stage, and prod
Each environment requires a distinct and independently maintained set of gateway controls. Shared configuration parameters create silent coupling between environments that typically surfaces during compliance audits rather than in routine testing. The table below outlines the key areas that must be configured separately across dev, staging, and production.
No row in this table should share a value across environments. If any configuration parameter is identical across development and production, the separation is incomplete and the control boundary is theoretical rather than enforced.
Deploying open banking APIs through the gateway pipeline
A structured CI/CD pipeline is the only reliable way to maintain environment separation at scale. Manual deployments create configuration drift and remove the audit trail that regulators expect. The deployment flow for open banking APIs should follow a defined promotion model with gates at each transition.
Step 1: Version environment-specific configurations in source control
Gateway configurations for each environment must be maintained in source control as separate, independently versioned files. Environment-specific variables including credentials, endpoint references, rate limit values, and consent scope definitions should be injected at deployment time from secure vaults. Storing these values as plain strings in shared configuration files removes the separation that versioning is intended to enforce.
Step 2: Validate in development before staging promotion
Before a build is promoted from development to staging, automated checks should confirm that the API contract matches the approved OpenAPI specification, that response schemas pass API contract testing validations, and that no development-only configuration values are referenced in the build output. Builds that reference development endpoints or relaxed credential scopes should fail automatically.
Step 3: Run compliance and governance checks in staging
Staging promotion should trigger automated PSD2 alignment checks, FAPI security validation, rate limit configuration verification, and API versioning consistency reviews. Consent scope configurations should be tested against realistic user consent flows before any code advances toward production. API governance policies, including schema enforcement and security standards, must pass before staging sign-off is granted.
Step 4: Enforce production promotion gates
Production deployment must require a reviewed approval step. The pipeline should block promotion if staging checks have not passed in full, if configuration mismatches are detected between the staging and production gateway definitions, or if credentials are not sourced from the production vault. This gate is the structural control that maintains API lifecycle management integrity across the entire release cycle.
What breaks open banking API environment separation
Teams managing open banking API deployments across environments encounter consistent failure patterns regardless of how well the architecture is documented. These gaps account for most of the environment bleed identified during pre-production reviews and compliance assessments, and they typically appear under deadline pressure rather than from deliberate design choices.
- Reusing OAuth client IDs across development and staging
- Applying production-level consent enforcement only after go-live testing instead of in staging
- Sharing logging pipelines across environments without PII redaction controls
- Skipping staging validation under release pressure and promoting directly from development
- Configuring environment-specific values as hardcoded strings in deployment scripts rather than injected secrets
- Using the same API keys for partner sandbox testing and internal development
Each shortcut creates a gap between documented architecture and operational reality. In regulated open banking deployments, gaps of this kind translate directly into audit findings, remediation cycles, and go-live delays that could have been avoided with disciplined environment controls applied consistently from the start of the deployment process.
How DigitalAPI supports open banking environment deployment
Deploying open banking APIs across isolated gateway environments requires more than pipeline discipline alone. Enterprises operating across multiple gateways need centralized governance and visibility across the entire estate without collapsing the environment boundaries that make isolation effective in the first place.
DigitalAPI operates as the governance and management layer above your existing gateways, whether you run Apigee, Kong, MuleSoft, or AWS API Gateway. It does not replace the gateway itself. Instead, it provides policy enforcement, lifecycle management, and sandbox enablement across your multi-environment estate.
Here is how DigitalAPI supports this:
- API governance with AI-powered policy enforcement, schema validation, OWASP checks, versioning discipline, and security standards applied consistently across environments
- API sandboxing that provides a safe pre-production testing environment, enabling teams to validate integrations without connecting to live production data
- Centralized monitoring and governance across multiple gateway environments through the API gateway manager
- Purpose-built open banking sandbox and marketplace infrastructure designed for compliance-ready financial API programs with PSD2 support
- Unified lifecycle management across discovery, cataloging, governance, and analytics through the API management platform
DigitalAPI gives banking teams centralized visibility and consistent governance across environments without requiring infrastructure consolidation or a rip-and-replace of existing gateways, preserving the separation already in place while adding a managed governance layer above it.
.png)
Frequently Asked Questions
1. What is environment separation in open banking API deployments?
Environment separation is the practice of maintaining independent gateway configurations, credentials, policies, and data paths for development, staging, and production. It ensures that testing activity cannot affect live consumer data, that compliance rules are enforced at the correct pipeline stage, and that production credentials are never accessible to development teams without explicit governance controls.
2. Why do open banking APIs require stricter environment controls than standard APIs?
Open banking APIs carry regulatory obligations under frameworks such as PSD2 and FAPI. Misconfigured policies, shared credentials, or incomplete consent enforcement can create compliance violations that are difficult to remediate after production deployment. The combination of financial data sensitivity and regulatory traceability requirements makes disciplined environment separation a structural requirement rather than a developer preference.
3. How should credentials be managed across development, staging, and production gateways?
Each environment must use distinct OAuth client IDs and API credentials scoped exclusively to that environment. Credentials should be stored in secrets vaults and injected at deployment time through the pipeline. No development credential should authenticate against staging or production endpoints, and production credentials must require explicit access approvals with a documented audit trail.
4. What should be validated in the staging environment before production promotion?
Staging validation should include API contract testing against the approved OpenAPI specification, FAPI and PSD2 policy alignment checks, consent scope enforcement testing, rate limit configuration verification, and security scans. Any failure in staging should block production promotion automatically through the pipeline rather than requiring a manual review gate after the fact.
5. How does a centralized API management platform help with open banking environment separation?
A centralized platform provides governance workflows, approval gates, and lifecycle visibility across all environments without requiring teams to manage each gateway independently. It enforces structured promotion from staging to production, maintains policy consistency checks, and manages sandbox environments that keep development and partner testing isolated from live production data paths.
You’ve spent years battling your API problem. Give us 60 minutes to show you the solution.
.svg)







.avif)
